In the Name of ALLAH the Most Beneficent and the Merciful
Hey, everyone here we are with yet another tutorial on SQLi, this one may not be very new but i am very sure many of the readers of securityidiots will enjoy reading the tutorial and learning something new with it. In this tutorial we ll learn Multiquery Injection, the injection which is many times misinterpreted as Routed Query Injection. When i was about to write on Routed query injection many of my friends asked me the difference between Routed query Injection and Multi Query Injection, i just told them to wait for the tutorials on both of them. Routed query injection has already been posted since a long time, but i wasnt able to get mysqlf some time to write on MultiQuery Injection, so now here we are.
First of all the basic difference between both of them:
In Routed query injection our payload gets injected in the first query and then the output of that query gets injected in the second query and so on.
In Multi query Injection we design our payload in such a manner that it can inject two or more queries with the same injection. No output from one query to another is passed in this scenario.
Testing for MultiQuery Injection, well its simple SQLi testing but in the end when we dont see any output from union based injection we can try and test for Multiquery injection, i have got a site which can be a good example fo Multiquery Injection for our tutorial.
Here is the B*tch we are gonna use through out this tutorial.
Now we can directly use Union select for that.
Its those days when i was addicted to figure out the reasons why some of the injections may not give you output even if everything is right, so i decided to keep trying.
After a while i saw something that even if we are invalidating the first query there was still some output which was coming from the first query, that can only happen in a case so i decided to check something.
And Boooooom!!!! it gave me another error.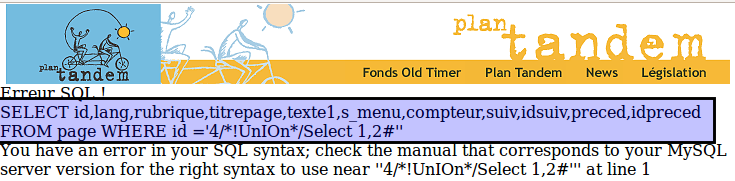
Now heres the basic logic of Multi Query Injection. We have multiple queries on that page when we inserted a single quote we got the error from first query but the first query was not giving any output. Now as we commented the first query we can write anything after comment and that wont create any error so when we inserted a single quote after comment, the first query passed and the second query is now getting injected, we can make it more simple as we can see there are eleven column in the query so we will first comment the first query and then inject the second one with eleven columns.
And congrats we got the printable column. Now rest of the part is simple like other injection.
Thats all for this tutorial, will catch you back soon with another tutorial.
Hey, everyone here we are with yet another tutorial on SQLi, this one may not be very new but i am very sure many of the readers of securityidiots will enjoy reading the tutorial and learning something new with it. In this tutorial we ll learn Multiquery Injection, the injection which is many times misinterpreted as Routed Query Injection. When i was about to write on Routed query injection many of my friends asked me the difference between Routed query Injection and Multi Query Injection, i just told them to wait for the tutorials on both of them. Routed query injection has already been posted since a long time, but i wasnt able to get mysqlf some time to write on MultiQuery Injection, so now here we are.
First of all the basic difference between both of them:
In Routed query injection our payload gets injected in the first query and then the output of that query gets injected in the second query and so on.
In Multi query Injection we design our payload in such a manner that it can inject two or more queries with the same injection. No output from one query to another is passed in this scenario.
Testing for MultiQuery Injection, well its simple SQLi testing but in the end when we dont see any output from union based injection we can try and test for Multiquery injection, i have got a site which can be a good example fo Multiquery Injection for our tutorial.
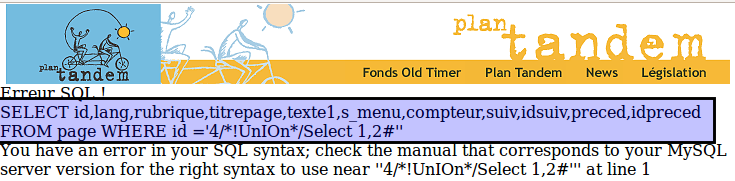
Here is the B*tch we are gonna use through out this tutorial.
http://www.plantandem.be/home.php?p=g&id=4
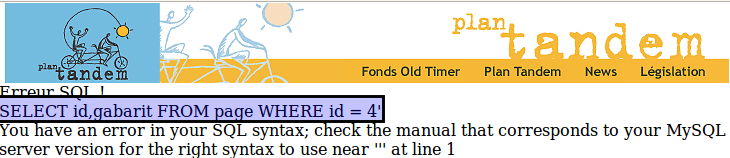
http://www.plantandem.be/home.php?p=g&id=4'
Now we can directly use Union select for that.
http://www.plantandem.be/home.php?p=g&id=4 and 0=1/*!UnIOn*/Select 1,2#
Its those days when i was addicted to figure out the reasons why some of the injections may not give you output even if everything is right, so i decided to keep trying.
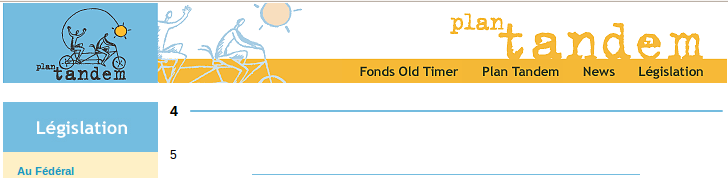
After a while i saw something that even if we are invalidating the first query there was still some output which was coming from the first query, that can only happen in a case so i decided to check something.
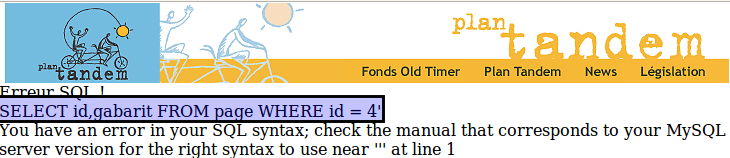
And Boooooom!!!! it gave me another error.
http://www.plantandem.be/home.php?p=g&id=4/*!UnIOn*/Select 1,2#'
Now heres the basic logic of Multi Query Injection. We have multiple queries on that page when we inserted a single quote we got the error from first query but the first query was not giving any output. Now as we commented the first query we can write anything after comment and that wont create any error so when we inserted a single quote after comment, the first query passed and the second query is now getting injected, we can make it more simple as we can see there are eleven column in the query so we will first comment the first query and then inject the second one with eleven columns.
http://www.plantandem.be/home.php?p=g&id=4#'and%20false/*!50000union*/select%201,2,3,4,5,6,7,8,9,10,11#'
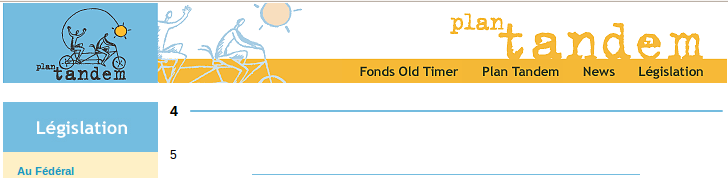
And congrats we got the printable column. Now rest of the part is simple like other injection.
Thats all for this tutorial, will catch you back soon with another tutorial.


